Open-source security
has been a hot topic in recent years, and it’s proven to be something
of a double-edged sword. On the one hand, there’s an understanding of
the potential that open-source tools hold for democratizing security,
making industry best practices accessible to more organizations and
helping keep everyone’s data better protected from attackers. On the
other hand, open-source codebases have been the subject of some of the
most serious and high-impact vulnerabilities we’ve seen over the past 12
months, namely Log4Shell and Spring4Shell.
While the feeling around open-source understandably wavers between
excitement and trepidation, one thing is for sure: Open-source
frameworks are here to stay, and it’s up to us to ensure they deliver on
their potential and at the same time remain secure.
The future of open-source was common theme at Black Hat 2022,
and two members of the Rapid7 research team — Lead Security Research
Spencer McIntyre and Principal Security Researcher Curt Barnard — shined
a light on the work they’ve been doing to improve and innovate with
open-source tools. Here’s a look at their presentations from Black Hat,
and how their efforts are helping push open-source security forward.
A more powerful Metasploit
Spencer, whose work focuses primarily on Rapid7’s widely used attacker emulation and penetration testing tool Metasploit,
shared the latest and greatest improvements he and the broader team
have made to the open-source framework in the past year. The upgrades
they’ve made reflect a reality that security pros across the globe are
feeling everyday: The perimeter is disappearing.
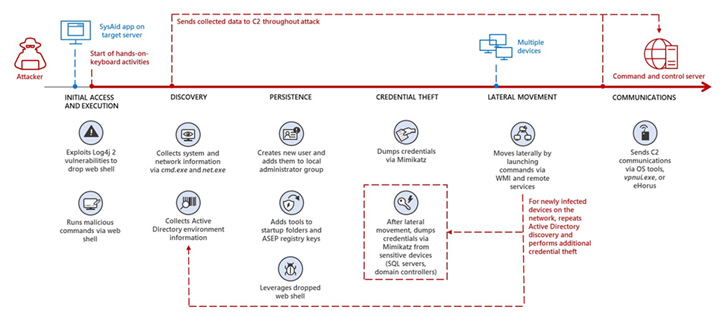
In a threat environment shaped by ransomware, supply chain attacks,
and widespread vulnerabilities like Log4Shell, bad actors are
increasingly stringing together complex attack workflows leveraging
multiple vulnerabilities. These techniques allow adversaries to go from
outside to within an organization’s network more quickly and easily than
ever before.
The updates Spencer and team have made to Metasploit are intended to
help security teams keep up with this shift, with more modern,
streamlined workflows for testing the most common attack vectors. These
recent improvements to Metasploit include:
****Credential capturing:**** Credential capture is a key component
of the attacker emulation toolkit, but previously, the process for this
in Metasploit involved spinning up 13 different modules and managing and
specifying configurations for each. Now, Metasploit offers a credential
capture plugin that lets you configure all options from a single
start/stop command, eliminating redundant work.
****User interface (UI) optimization:****URLs are commonly used to
identify endpoints — particularly web applications — during attacker
emulation. Until now, Metasploit required users to manually specify
quite a few components when using URLs. The latest update to the
Metasploit UI understands a URL’s format, so users can copy and paste
them from anywhere, even right from their browser.
****Payloadless session capabilities:****When emulating attacks,
exploits typically generate Meterpreter payloads, making them easy to
spot for many antivirus and EDR solutions — and reducing their
effectiveness for security testing. Metasploit now lets you run
post-exploitation actions and operations without needing a payload. You
can tunnel modules through SSH sessions or create a WinRM session for
any Metasploit module compatible with the shell session type, removing
the need for a payload like reverse shell or Meterpreter.
****SMB server support:**** Metasploit Version 6 included SMB 3
server support, but only for client modules, which was limiting for
users who were working with modern Windows targets that had disabled SMB
3 client support. Now, SMB 3 is available in all SMB server modules, so
you can target modern Windows environments and have them fetch (often
payload) files from Metasploit. This means you don’t need to install and
configure an external service to test for certain types of
vulnerabilities, including PrintNightmare.
Defaultinator: Find default credentials faster
Metasploit is at the heart of Rapid7’s commitment to open-source
security, but we’re not stopping there. In addition to continually
improving Metasploit, our research team works on new open-source
projects that help make security more accessible for all. The latest of
those is Defaultinator, a new tool that Curt Barnard announced the
release of in his Black Hat Arsenal talk this year. (Curt also joined
our podcast, Security Nation, to preview the announcement — check out that episode if you haven’t yet!)
Defaultinator
is an open-source tool for looking up default usernames and passwords,
providing an easy-to-search data repository in which security pros can
query these commonly used credentials to find and eliminate them from
their environment. This capability is becoming increasingly important
for security teams, for a few key reasons:
- Some commonly used pieces of hardware in IT environments come with
default credentials that could give attackers an easily exploitable
method of network access. Curt gave the example of the Raspberry Pi
microcontroller board, which always comes with the username “pi” and
password “raspberry” for initial login — a security flaw that resulted
in a 10 CVSS vulnerability published in 2021.
- Meanwhile, IoT devices have been proliferating, and many of these
manufacturers don’t have security best practices at the front of their
mind. That means hardcoded default credentials for first-time logins are
common in this type of tool.
- Many software engineers (Curt included) spend a lot of time in Stack Overflow,
and many of the code snippets found there contain example usernames and
passwords. If you aren’t careful when copying and pasting, default
credentials could make their way into your production environment.
With a whopping 54 CVEs for hardcoded usernames and passwords
released just in 2022 so far (by Curt’s count), security pros are in
need of a fast, accurate way to audit for default credentials. But until
now, the tools for these kinds of audits just haven’t been out there,
let alone widely available.
That’s why it was so important to make Defaultinator, the first tool
of its kind for querying default usernames and passwords, an open-source
solution — to ensure broad accessibility and help as many defenders as
possible. Defaultinator offers an API search-based utility or a
web-based user interface if you prefer not to interact with the API. It
runs in Docker, and the quickstart repository on Github takes just four lines of code to get up and running.





![[Image: igtKaQW.png]](https://external-content.duckduckgo.com/iu/?u=https://i.imgur.com/igtKaQW.png)